MILG-POPS
MIDDLE EAST;MILITARY; INTELLIGENCE
Tuesday, December 8, 2020
Saturday, December 5, 2020
Friday, December 4, 2020
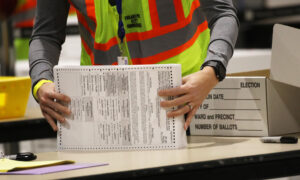
Arizona Legislature Calls for Immediate ‘Forensic Audit’ of Dominion Voting Machines
The Arizona House and Senate have called for an audit of the Maricopa County election software and equipment following allegations of fraud and other irregularities presented by President Donald Trump’s team earlier this week.
In a news release Friday, GOP leaders of the Republican-controlled legislature sought an independent audit of Dominion Voting Systems software—used in Maricopa County—called for the audit.
State Sen. Michelle Ugenti-Rita, a Republican said that Maricopa County’s Board of Supervisors “is supportive of conducting an independent audit of their voting software and equipment,” adding: “It is important we maintain all of the voting public’s confidence in our elections, and this is a positive step.”
House Majority Leader Warren Petersen, a Republican, said that “a significant number of voters believe that fraud occurred,” citing “the number of irregularities” that allegedly occurred in Maricopa County and elsewhere in the state.
“Especially concerning,” he said, “are the allegations made surrounding the vendor Dominion,” adding that the county needs to carry out a “forensic audit on the Dominion software to make sure the results were accurate.”
The Epoch Times has reached out to Dominion for comment following Petersen’s statement. Maricopa County has not immediately responded to a request for comment.
FOR IMMEDIATE RELEASE: Legislative Leaders call for audit of Maricopa County election software and equipment #AZSenate #AZleg #Election @AZHouseGOP pic.twitter.com/wDlr7v0fDT
— AZSenateRepublicans (@AZSenateGOP) December 4, 2020
Previously, Dominion’s CEO and a spokesman have said it’s not possible to change votes from one candidate to another, as some witnesses claimed in affidavits and in legislature hearings across the United States. They also denied being able to monitor, in real-time, the tabulation of votes and have also denied that Dominion employees have access to the tabulation efforts, saying only county employees do.
In the letter, Petersen was joined by Senate President Karen Fann, a Republican, in calling on the county to audit the results.
Their statement said that Maricopa supervisors have to “move expeditiously” on the forensic audit. The Electoral College will vote to certify the election on Dec. 14.
On Monday, Maricopa GOP Chairwoman Linda Brickman, for example, told the Legislature in an event hosted by President Donald Trump’s lawyers, saying that she and her Democratic partner saw “more than once” Trump votes default and shift to Joe Biden as they were entering votes into Dominion machines from ballots that the machines couldn’t read.
“I observed, with my Democratic partner, the preparation of a new ballot, since the original one was soiled, or wouldn’t go through the tabulators. I read her a Trump Republican ballot, and as soon as she entered it into the system, the ballot defaulted on the screen to a Biden Democratic ballot,” Brickman told lawmakers on Monday. She said that her testimony was submitted in a sworn affidavit under perjury.
“We were never told what, if any corrective action was taken,” Brickman asserted. “All I know is the next day, I was called outside the room that I was working in for signature verification by a supervisor who said, ‘I understand you caused some problems this week and you thought our machines were not working correctly.”
Previously, Trump’s legal team and other lawyers have alleged that Dominion systems are compromised, which triggered a bevy of counter-statements from Dominion that they’re false.
Arizona Legislature Calls for Immediate ‘Forensic Audit’ of Dominion Voting Machines
The Arizona House and Senate have called for an audit of the Maricopa County election software and equipment following allegations of fraud and other irregularities presented by President Donald Trump’s team earlier this week.
In a news release Friday, GOP leaders of the Republican-controlled legislature sought an independent audit of Dominion Voting Systems software—used in Maricopa County—called for the audit.
State Sen. Michelle Ugenti-Rita, a Republican said that Maricopa County’s Board of Supervisors “is supportive of conducting an independent audit of their voting software and equipment,” adding: “It is important we maintain all of the voting public’s confidence in our elections, and this is a positive step.”
House Majority Leader Warren Petersen, a Republican, said that “a significant number of voters believe that fraud occurred,” citing “the number of irregularities” that allegedly occurred in Maricopa County and elsewhere in the state.
“Especially concerning,” he said, “are the allegations made surrounding the vendor Dominion,” adding that the county needs to carry out a “forensic audit on the Dominion software to make sure the results were accurate.”
The Epoch Times has reached out to Dominion for comment following Petersen’s statement. Maricopa County has not immediately responded to a request for comment.
FOR IMMEDIATE RELEASE: Legislative Leaders call for audit of Maricopa County election software and equipment #AZSenate #AZleg #Election @AZHouseGOP pic.twitter.com/wDlr7v0fDT
— AZSenateRepublicans (@AZSenateGOP) December 4, 2020
Previously, Dominion’s CEO and a spokesman have said it’s not possible to change votes from one candidate to another, as some witnesses claimed in affidavits and in legislature hearings across the United States. They also denied being able to monitor, in real-time, the tabulation of votes and have also denied that Dominion employees have access to the tabulation efforts, saying only county employees do.
In the letter, Petersen was joined by Senate President Karen Fann, a Republican, in calling on the county to audit the results.
Their statement said that Maricopa supervisors have to “move expeditiously” on the forensic audit. The Electoral College will vote to certify the election on Dec. 14.
On Monday, Maricopa GOP Chairwoman Linda Brickman, for example, told the Legislature in an event hosted by President Donald Trump’s lawyers, saying that she and her Democratic partner saw “more than once” Trump votes default and shift to Joe Biden as they were entering votes into Dominion machines from ballots that the machines couldn’t read.
“I observed, with my Democratic partner, the preparation of a new ballot, since the original one was soiled, or wouldn’t go through the tabulators. I read her a Trump Republican ballot, and as soon as she entered it into the system, the ballot defaulted on the screen to a Biden Democratic ballot,” Brickman told lawmakers on Monday. She said that her testimony was submitted in a sworn affidavit under perjury.
“We were never told what, if any corrective action was taken,” Brickman asserted. “All I know is the next day, I was called outside the room that I was working in for signature verification by a supervisor who said, ‘I understand you caused some problems this week and you thought our machines were not working correctly.”
Previously, Trump’s legal team and other lawyers have alleged that Dominion systems are compromised, which triggered a bevy of counter-statements from Dominion that they’re false.